Frequently Asked Questions
Getting help
Requests for technical assistance and other issues related to Check-in can be obtained by sending an email to:
Alternatively, if you already have a Check-in account, the EGI Helpdesk can be used. More information can be found in the Helpdesk documentation. In that case, submit a new ticket and make sure that the support unit is assigned to “Check-in (AAI)”.
Connect to Check-in an IdP federated in an hub and spoke federations
I get an error similar to: “Error - EGI Check-in Service not accessible through your institution” (SURFconext example)
In case of a “hub and spoke” federation the federation coordinator may require that the IdP administrators explicitly request to connect to a SP and let their users to authenticate on these SP.
In most of the cases this is not a configuration problem neither for the Check-in service nor for the Identity provider. The connection needs to be implemented in the hub and spoke IdP Proxy.
One example of such federation is SURFconext, the national IdP federation for research and education in the Netherlands operated by SURFnet. If you are using credentials from a Dutch IdP in eduGAIN, the SURFconext administrator of your institute needs to request the connection.
Authentication error with ADFS-based Identity Providers
Why do I get the error below after successfully authenticating at my Home IdP?
opensaml::FatalProfileException at (https://aai.egi.eu/registry.sso/SAML2/POST)
SAML response reported an IdP error.
Error from identity provider:
Status: urn:oasis:names:tc:SAML:2.0:status:Responder
The Responder error status is typically returned from ADFS-based IdP
implementations (notably Microsoft ADFS 2.0 and ADFS 3.0) that cannot properly
handle
Scoping elements.
Check-in can be configured to omit the scoping element from the authentication
requests sent to such IdPs in order to allow successful logins. Please send an
email to the Check-in Support team using checkin-support <AT>
mailman.egi.eu and include a screenshot of your error.
I have linked an IGTF X.509 certificate to my Check-in identity but the information is inaccurate or incomplete
What can I do?
To update your certificate information, follow these steps to log into your Check-in profile page using your IGTF certificate:
- Click here to access your profile page
Warning
This may log you out of any service you have accessed with Check-in on this browser!Warning
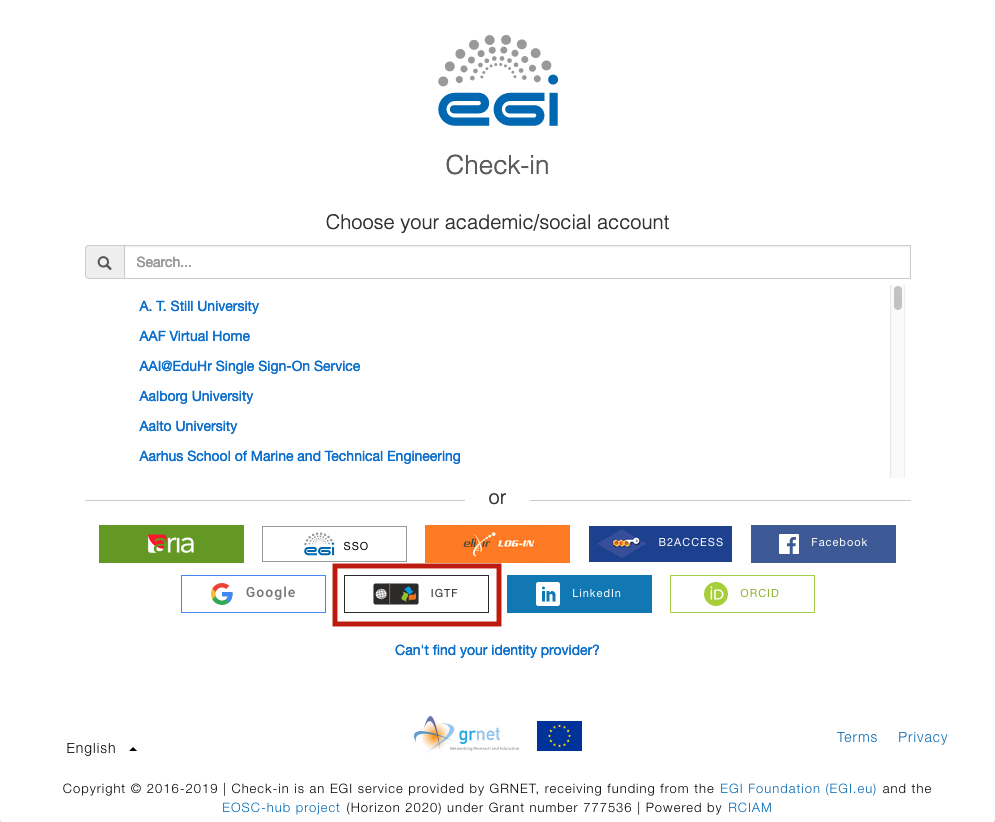
If prompted to log in with a different identity provider, click CHOOSE ANOTHER ACCOUNT and then select IGTF. Alternatively, you can click here for your convenience